Scaling up Binary Exploitation Education
Augmenting Esoteric Security Subjects with Gamification & Accessibility
The shortage of proficient cyber operators in a world now dependent on connectivity and information has left nations scrambling to build capabilities in a volatile and high stakes race for digital arms. Despite the availability of near infinite capital, the industry finds itself bottlenecked by a scarcity of experts. This deficit has been further aggravated by the increasing complexity of the field, and lack of upstream educational investments.
As strong advocates of security education, we’ve dedicated time towards developing a number of unique technologies to help address this widening deficit. We demonstrate how these tools can be used to educate larger, less specialized demographics, improve student-autonomy, and scale the security workforce to meet market demands.
Learning Curve
Programming languages are the human friendly medium that software developers use to tell computers what to do. The average developer does not need to understand their software at a level lower than their own code. The purpose of human friendly abstractions is to hide the underlying complexity.
In contrast, the subjects of software security (with regard to binary exploitation) are difficult to learn without an intimate understanding of that ‘underlying complexity’. The bar for entry demands an inordinate level of familiarity with obtuse low level software concepts, operating systems, CPU architecture, debuggers, disassemblers, and more.
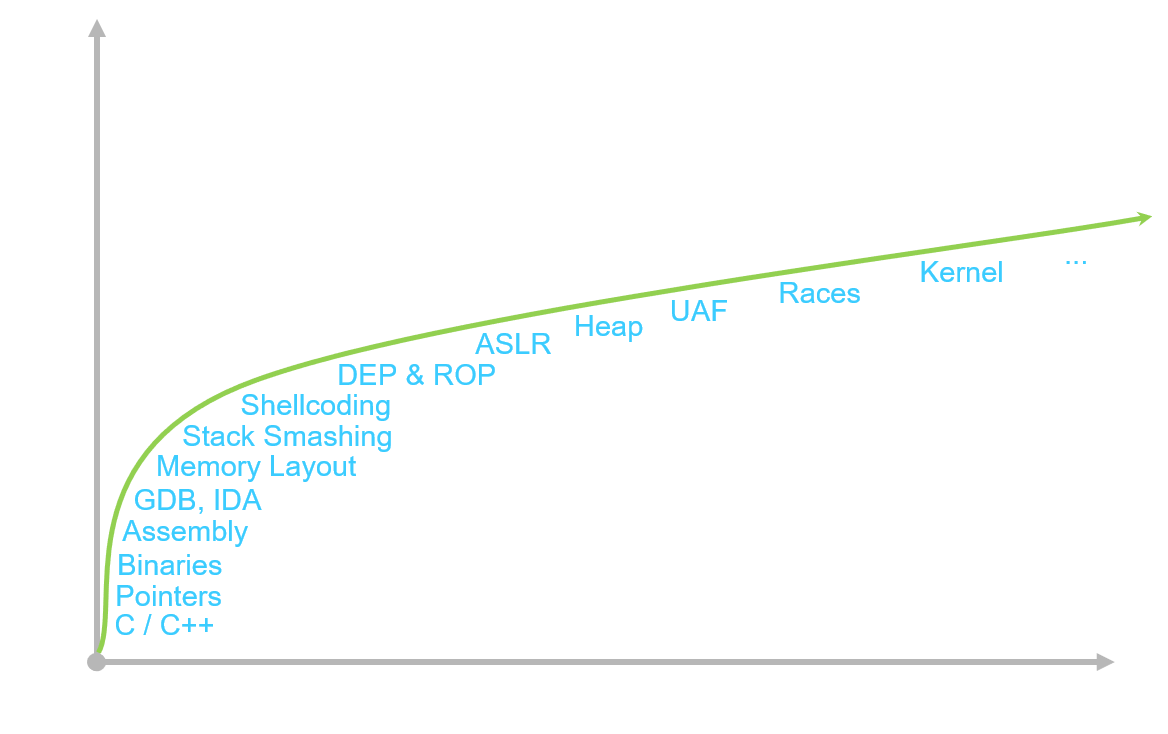
The learning curve to binary exploitation is steep, demanding a solid understanding of low level fundamentals
This depth of computer literacy can be intimidating to even senior software engineers. But when bundled and applied properly, exploit developers use this suite of knowledge to ‘surf on the fringe of what is possible’, opening doors to software and systems that were never intended to exist.
As modern software security continues to evolve, this learning curve only grows more daunting.
Exploit Education
Almost exclusively, these skills are learned informally through years of self-study and careful review of existing research. The ambitious few who overcome the steep learning curve will often find their footing with wargames.
In the security community, the term ‘wargame’ typically refers to a series of challenges that hone and refine one’s technical skills. This is where most newcomers take their first steps into the world of security. Over the past decade, a number of wargames have grown quite popular including IO NetGarage, Pwnable.kr, and OverTheWire (among others).
Traditional exploitation based wargames often require players to ssh into an open (educational) linux server that hosts the wargame’s challenge binaries. By exploiting the first challenge, players will gain access to a protected flag file that contains the password to the next level, allowing them to login to the next level and continue the game.
The problem with using these resources for self-guided education is that there often isn’t a clear understanding of what knowledge is required to complete a given challenge. On top of that, the metric for success is often black and white, making it hard for players to know if they are progressing down the right path or simply wasting their time.
Finally, the breadth of subjects covered by these challenges (while interesting) can vary wildly in quality, scope, and narrative. The knowledge learned from solving one puzzle is often disjoint from the next. The inherent volatility can be jarring for someone who is unfamiliar with this framework of learning.
Like crossword puzzles, many security wargames have been designed to challenge users - not to teach them. Their use as an educational resource has grown simply due to the lack of better alternatives.
Next Generation Wargaming
As the culmination of several years spent teaching these deeply technical subjects, we are familiar with the shortcomings of existing resources. We collaborated with Rensselaer Polytechnic Institute for the Spring 2018 semester to deliver a course that promised a new and innovative take on traditional exploit education.
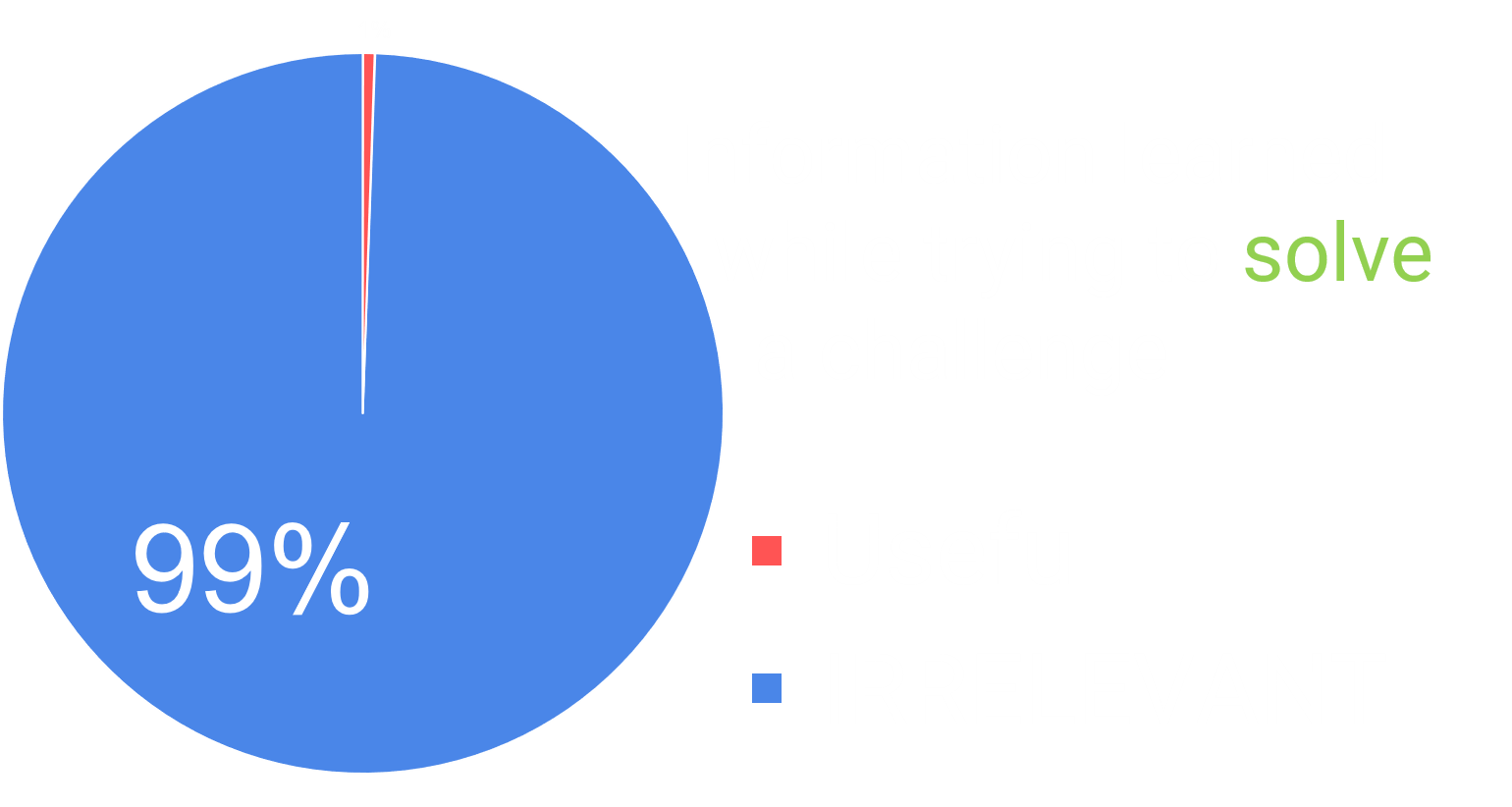
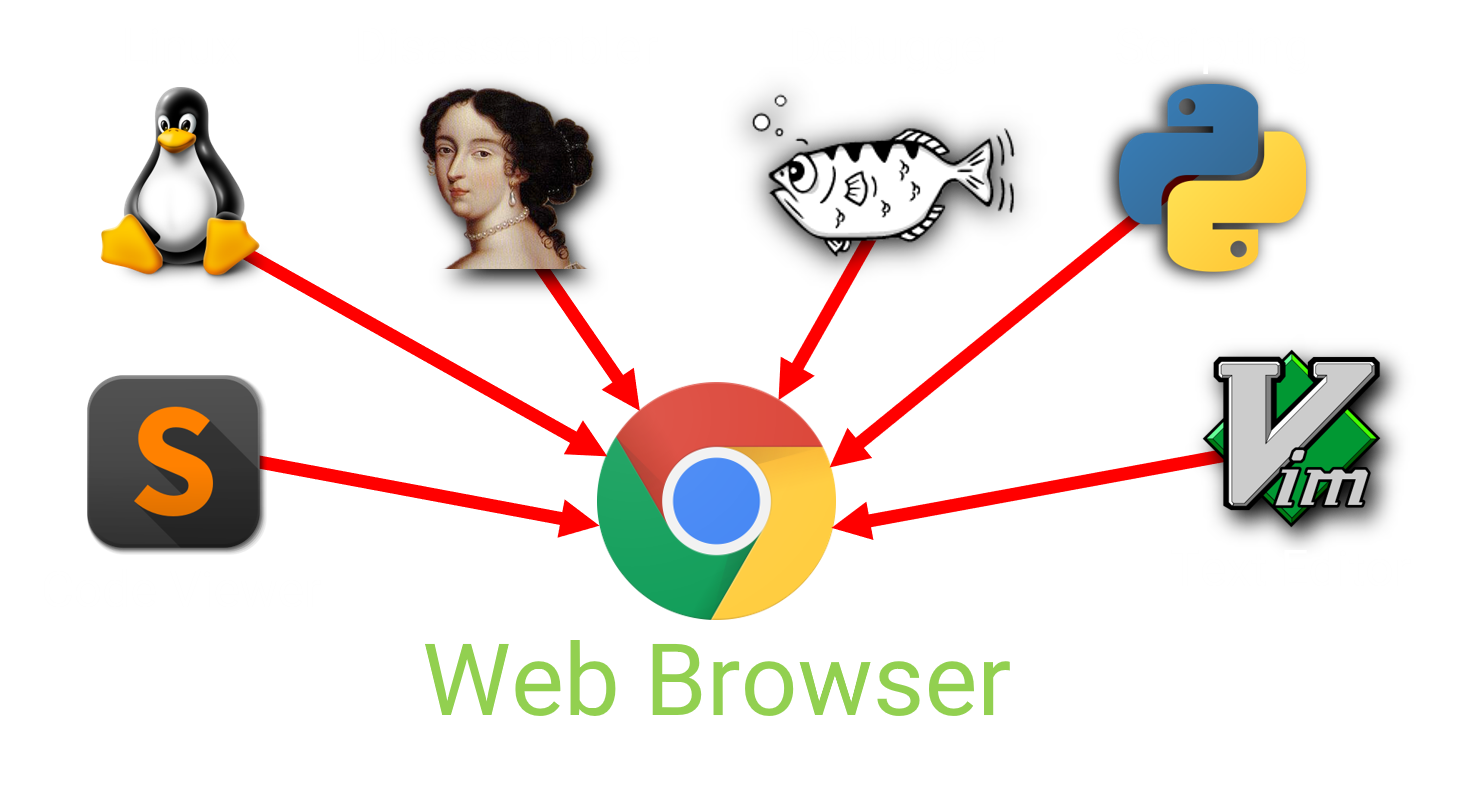
Serving as a replacement to the existing Modern Binary Exploitation course by RPISEC, we wanted to build a new experience that could encapsulate the industry-standard exploit development workflow into a single browser tab.
This eliminates the need for our students to acquire any specialized software or hardware, while ensuring everyone works in an identical environment. From any laptop or workstation, a student could simply plug in the URL to our educational wargame and start playing in seconds.
The ubiquity of this approach has made the platform an ideal solution for leading workshops, security trainings, or even semester long university courses. But this is only how it starts.
Our core experience is built around a gamified ‘lab workspace’ that simulates the aforementioned exploit development workflow. This is where students will spend most of their time engaging with the platform, following lecture examples, performing lab work, or completing course projects.
Without the need for multiple VM’s, extraneous resources, or specialized skills - it is effortless to get students started.
For the purpose of this post, we have made available an interactive preview of the lab workspace. The linked preview is a binary we use to introduce students to stack smashing early on in the course. For the purpose of the preview, we added a few additional prompts to help you find your way around.
In the following section, we will talk a bit more about some of the platform’s features, and how we have used it as a natural extension of the classroom.
The Lab Workspace
The browser based lab workspace consists of multiple different views that evolve over the flow of the course. The tools exposed in these views integrate directly with each other to provide a seamless and self-contained playground for students to explore and grow within.
Our goal was to teach students practical skills in binary exploitation while exposing them to true-to-life tooling. In the following sections, we highlight some of the views and tools that are central to this experience.
Debugger
On the right side of the lab workspace is the ‘wargame debugger’ or wdb. From this terminal, students can debug the lab and lecture binaries much like you would on a modern linux system.
This command line debugger is modeled off of gdb, offering 1-for-1 parity for the commands used most frequently on wargame challenges, CTF binaries, and real world targets. Its scope has been reduced to focus on assembly level debugging, a necessary skill for reverse engineering & binary exploitation.
Disassembler
On the left side of the lab workspace is an interactive disassembler that is synchronized with the debugger. Analogous to the industry-standard offerings of IDA Pro or Binary Ninja, students can use this disassembler to explore, annotate, and reverse engineer the assembly code of the compiled lab binaries.
The in-browser disassembler can switch between linear disassembly and graph views using the SPACE key. Assembly-level comments can be placed using the ; (semicolon), while the TAB key can be used to flip between assembly instructions and their corresponding source lines.
Additionally, the disassembler supports function renaming, g for goto, and x for Xrefs.
Provisioning students with an in-platform disassembler encourages the naturally curious to build a deeper understanding of low level systems. For a reverse engineering heavy course, there is no question that a disassembler is an integral part of the workflow.
Code Viewer
When teaching binary exploitation, we provide students with the source code to the large majority of the lab binaries so they can focus solely on learning about vulnerability classes, mitigations, and exploit techniques.
When available, the source for the current lab binary is provided in the Source tab of the lab workspace:
Python Scripting
Finally, the lab workspace includes a limited but capable Python runtime. This is exposed as a Python terminal that students can sketch code snippets into, and a fully fledged code editor beneath it. Within the code editor, students can write python to script interaction with the lab binary over STDIN and STDOUT.
As the course progresses, students will have to write increasingly complex exploit scripts in Python to solve each challenge. These exploits are used to drive the lab binaries through carefully crafted input, producing a shell on the exploited system if successful.
Course Gamification
While designing this platform, we employed a number of gamification techniques to improve student autonomy and depth of understanding. One of the most powerful elements of this gamification resides within these little breadcrumbs we call checkpoints at the bottom right of the lab workspace.
Checkpoints serve as a roadmap for students by providing them feedback through incremental goals towards successful exploitation of the lab binary. This helps students feel less lost about where to go, or what to focus on while attempting to break down each lab.
At the end of each level is a protected flag file. If the student can exploit the target binary and gain complete control (a shell) on the vulnerable system, they will be able to cat the flag file indicating successful compromise.
Running a completed python exploit script to get a shell & capture the flag from within the lab workspace
The benefits we found from even basic gamification of otherwise tedious material captivated students, dramatically increasing participation and comprehension. Backed by powerful binary emulation & introspection technology, we are constantly exploring new and innovative ways to provide students actionable feedback through the platform.
Technology In Practice
The platform-based binary exploitation course offered at RPI helped to refine the educational experience outlined in the sections above. The coursework consisted of ten labs assignments, two projects, and over 50 exploitable binaries that were used to teach various subjects of modern x86_64 linux exploitation.
The students were a diverse mix of CS/CSE/EE/IT degrees (freshman to graduate) with little to no prior experience in security. We observed that the course executed much smoother than any of our past classes or workshops, resulting in students who were able to synthesize elegant solutions to complex tasks quicker than we had seen previously.
Bit by the security bug, a number of these students went on to accept full-time opportunities related to cyber. One student inquired about interning under us at RET2 for the summer, discovering two exploitable macOS kernel vulnerabilities over the duration of his internship.
This course is used to build foundational skills in binary exploitation, empowering student interest into these subjects of security. Once past the initial learning curve, practical skill transfer and growth becomes instinctive rather than taught.
Broader Application
A curriculum on binary exploitation is only the first of many ways we could have leveraged this platform. This technology can be adapted to teach a variety of non-security topics too, including C-programming, operating systems, computer architecture, embedded systems, or other less-niche subjects.
When presented properly, games can be used to mask extremely technical problems as human friendly puzzles. The illusion of a game helps attract and retain less-specialized demographics (at any age or skill level) to solve problems that they might otherwise consider themselves unqualified for.

Shenzen I/O is a popular programming-puzzle game that revolves around circuit design & assembly code
The growing popularity of highly technical games (c.f Shenzen I/O, TIS-100, EXAPUNKS, 0x10c, …) has shown that these topics can appeal to a broader audience. In security research, the industry has begun to experiment with using games to augment the vulnerability discovery process, further legitimized by the launch of DARPA’s own CHESS.
Our experience has shown that traditionally esoteric security subjects can be learned more efficiently through the use of games. And without requiring specialized software or hardware, the ability to scale both interest and participation into these niche subjects from a dozen to thousands is easy, if not natural.
Conclusion
We have only begun to scratch the surface on the utility and impact of this educational technology. There are few resources dedicated (or capable) to help ‘grow’ the security workforce at large, and the increasing complexity of this industry has made it almost impossible for newcomers to enter the field.
For these reasons, we have begun collaborating with other industry partners and educational institutions to help make these resources readily available. If you think this technology can complement your organization in a meaningful way, please feel free to contact us. We welcome the conversation.